- Home
- Technologies
- DOCSIS and EuroDOCSIS
DOCSIS® and EuroDOCSIS® testing
Speed up your DOCSIS® testing, lower your testing costs and make sure that your products meet your customers’ needs: entrust your DOCSIS® pre-certification, and other compliance testing to our experts. Looking for related testing solutions? We’ve got you covered!
The widest range of testing services
Whether you are using EuroDOCSIS, DOCSIS 3.0 or 3.1 or are preparing for the upcoming 4.0 version; whether you need to test a modem, CMTS, CCAP, Remote PHY Device, CMTS core or an amplifier: we work with you to navigate the tricky testing process quickly and effectively.
From defining product requirements to designing, automating, and executing acceptance and regression tests: we help and support where you lack the resources or expertise. Our lab has the CMTSs, modems, RF measurement equipment, DOCSIS protocol analyzer and traffic generators to perform the testing. Furthermore our +20 years of experience in DOCSIS testing make us the preferred partner of many in the industry.
Our test scope includes certification readiness, RF performance, stability, throughput, and interoperability.
PacketCable, Gateway and L2VPN testing
Requirements for home gateway devices are as diverse as the markets in which they are deployed. We have the experience, expertise and infrastructure to help you define your specific requirements and perform extensive tests before your devices are built or deployed.
Our expertise is broad; from voice technology to country-specific POTS needs and from business services to multi-operator deployments.
LTE immunity and environmental testing
You don’t want your customers to struggle with LTE interference or other phenomena that degrade your DOCSIS service when they are in the field, do you?
Our LTE Immunity certification program makes sure your service is not affected by wireless signals in the same spectrum.
Large-scale stability and audit testing
A large-scale stability set-up for regression testing in your own lab is expensive to build, automate and maintain.
Yet why should you do it yourself? We have the expertise, the equipment, and the testbeds, fully wired up to high-throughput traffic generators – to ensure more value for money and quicker turnaround.
- How can we help you ?
Excentis is an expert team of network, hardware and software engineers, testers and trainers, with decades of lab and field experience, a passion for optimization, automation and natural aversion to latency. How can we help?
Jan De Beule
EMEA
Charlie Viaene
AMER/APAC
Cases
World premiere: Excentis supports first live DOCSIS 4.0 test by Liberty Global & VodafoneZiggo with traffic generation and live dashboards
- ByteBlower
- DOCSIS
- DOCSIS 4.0
- Latency
- Testing
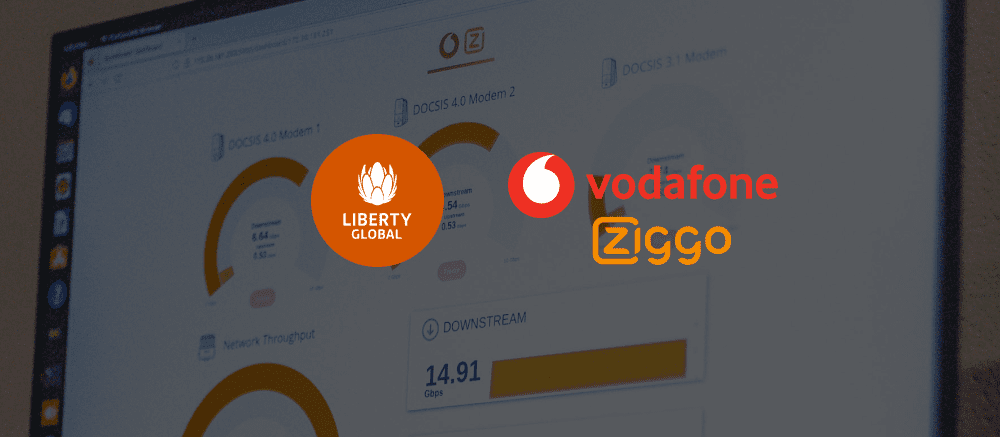
World premiere: Excentis supports first live DOCSIS 4.0 test by Liberty Global & VodafoneZiggo with traffic generation and live dashboards
Explore this caseBouygues Wi-Fi 6E gateway and CPE device testing with ByteBlower
- ByteBlower
- Testing

Bouygues Telecom selected ByteBlower to test its Bbox portfolio of CPE devices and validate their performance and continuously validate new functionality on their existing Bbox solutions and test completely new CPEs, like the latest Bbox ultym that supports Wi-Fi 6E.
Explore this caseLow Latency DOCSIS training for Virgin Media O2
- DOCSIS
- Low Latency DOCSIS
- Training
Customer case: how we helped Virgin Media gain insight into Low Latency DOCSIS (LDD) testing and improvement through theoretical and practical training.
Explore this caseHome Gateway Testing
- Testing
- Wi-Fi

Cable operators are deploying advanced home gateways instead of simple cable modems. New advanced services, the transition to IPv6 and the ever increasing number of connected devices push such gateways to support a multitude of services and devices — fundamentally increasing development time and deployment complexity.
Explore this caseWe’re proud to work for the best in the world











Testimonials
What Our Customers Say About Our Service
Optimized parameters not only resulted in a boost in overall performance, PŸUR even scored a whopping 100% in Download and Upload Data Tests.
Thomas Anders
Director of Engineering at PYUR

No new investment was needed to test Wi-Fi 6E, ByteBlower wireless endpoints are compatible with new devices out-of-the-box. Wi-Fi 7 will be no different!

Russell Bean
Manager IP Operations at Cable & Wireless
The Excentis training course exceeded our high expectations. In depth yet accessible to a broad audience. Technical topics but never boring!

Endika Miragaya
Delivery Manager at Vodafone Group Services Düsseldorf

Thank you for your excellent work. We found the report very interesting and were happy to see the quality of choices quantified and objectively confirmed.

Henrik Häggman
Product Manager for Broadband Services at Tele2, Sweden

With support of the Excentis engineering team, we constructed an initial setup and successfully performed a first trial run in less than an hour!
Proximus In-Home Solutions Team
Proximus In-Home Solutions Team
With professional guidance and willing to adapt to our specific needs, we could test the device in a way that makes most sense to our customers. We highly recommend them for your business.

Martin Åberg
Strategic Product Manager Broadband & Proptech, Telenor Sverige AB


