The operation of Wi-Fi bridges
Wi-Fi has become the preferred technology for in-home connectivity, but sometimes it’s needed to connect a wired device (e.g. a printer) to a Wi-Fi network using a Wi-Fi bridge. In a wired world bridges are used very often and typically don’t cause much problems. In the Wi-Fi world the situation is slightly different, read on and find out why!
The operation of Wi-Fi
The Wi-Fi environment is a challenging environment, due to the unpredictable and very variable quality of the wireless link. Therefore it was decided to implement, on the wireless link itself, a mechanism to make sure packets that were lost in the transmission are retransmitted. As a consequence every packet that is transmitted on the wireless link needs clear identifiers which wireless device transmitted the packet and which wireless device is the intended receiver.
Wi-Fi was also invented at a time that every bit that was transmitted, counted. Over low bit-rate links, any extra bit not only causes the effective throughput to be smaller, but also introduces additional latency.
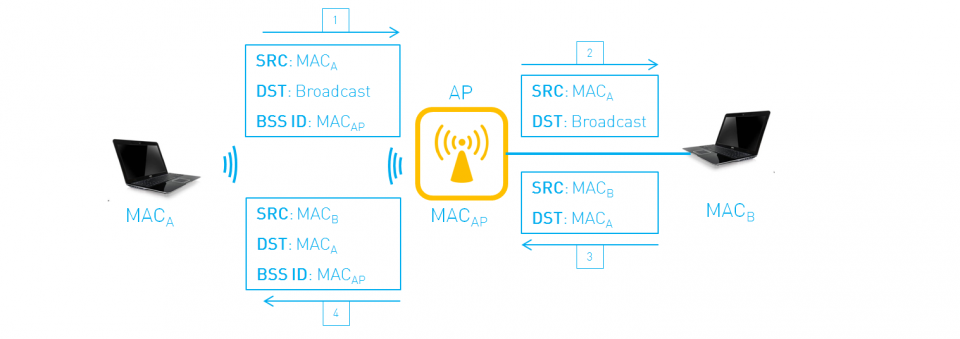
As a consequence of the above two reasons, standard Wi-Fi uses three MAC addresses on the wireless link, as illustrated in the figure below. One of the MAC addresses contains the BSSID, this one identifies the Wi-Fi network. The example below shows the addresses in use when a broadcast packets (e.g. an ARP request) is sent by the device with MAC address A.
Let’s now consider the situation that a Wi-Fi client is bridging packets. This situation is illustrated below.
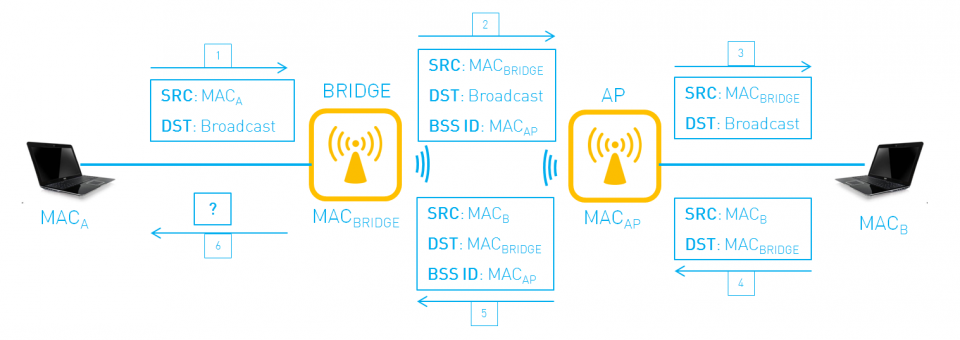
On the wireless link MAC address A is not in the packet anymore, as a consequence the receiver will reply to the MAC address of the bridge and, unless the bridge does some tricks, the bridge does not know where to send packet 5. As a consequence, communications between A and B will not be possible.
What are the solutions?
NATting at the Wi-Fi bridge
A possible solution, implemented by some devices, is shown below. The Wi-Fi bridge implements a NAT-function which means that the Wi-Fi bridge replaces the source IP address of A by its own IP address. By storing information of the outgoing packets (e.g. protocol and port numbers, ICMP identifier) it can map the response to the request on the Wi-Fi link back to the IP address of the original outgoing request.
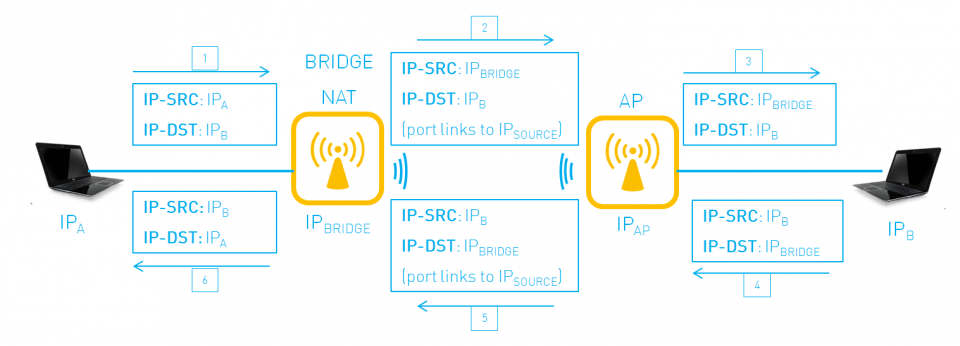
Of course, NATting can introduce other problems, as explained in our blog post about NAT.
MAC address spoofing
Another solution that is used is shown in the figure below:
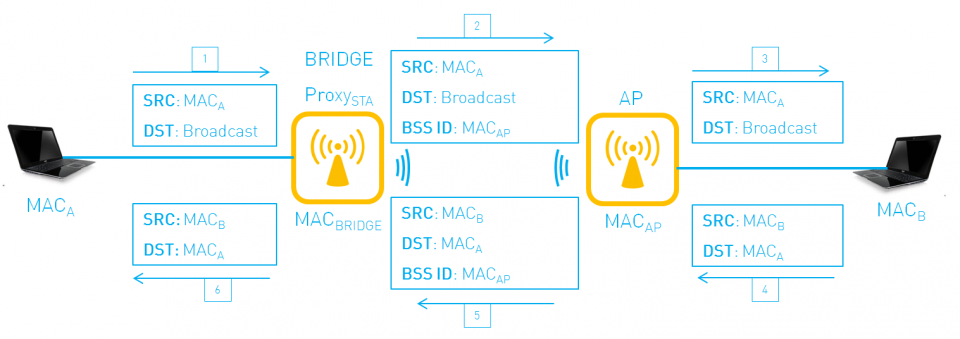
In this case the Wi-Fi bridge sets up a new association on the Wi-Fi link for each attached MAC address. The Wi-Fi bridge spoofs the MAC address. In this scenario each device behind the Wi-Fi bridge will have its own Wi-Fi association. An implementation of this is typically limited by the number of MAC addresses it can spoof. If security on the Wi-Fi link is enabled (WPA/WPA2), the Wi-Fi bridge also needs to perform the 4-way security handshake for each newly detected MAC address, which results in even more overhead.
In this solution it is important to realize that the AP will actually detect multiple MAC addresses on the Wi-Fi link, one for each device behind the Wi-Fi bridge.
Wireless Distribution System (WDS)
The cleanest solution is of course to use 4 MAC addresses on the link between Wi-Fi bridge and Wi-Fi AP. This method of operation is used in the WDS (Wireless Distribution System). Although the WDS architecture is mentioned in the standard Wi-Fi specification, its use cases are not described and it cannot be used in general since it requires support of the Wi-Fi AP.
Conclusion
Since the original design of Wi-Fi did not take into account the use case of a Wi-Fi bridge, using a Wi-Fi bridge can be troublesome. Different solutions exist to cope with this limitation and we explained them in this blog post.



























